
How Data Security and Privacy Can Save Corporations Money
Successful corporations hold the trust of their clients: it is the responsibility of the corporation to hold a client’s data securely and to protect their

Successful corporations hold the trust of their clients: it is the responsibility of the corporation to hold a client’s data securely and to protect their

Customer identity and access management (CIAM) is taking over the customer login experience. There’s more at stake than just registration and authentication. If all you’re

As transactions made over online stores and e-commerce websites always necessitate the exchange of sensitive details like credit card number and PINs etc., such details

Running a business without adequate data security is a massive risk. Crippling data breaches are increasingly common and no business is immune. In 2018, Dubai’s fastest

For new digital business models to succeed, customers’ privacy preferences need to be secure, and that begins by treating every identity as a new security
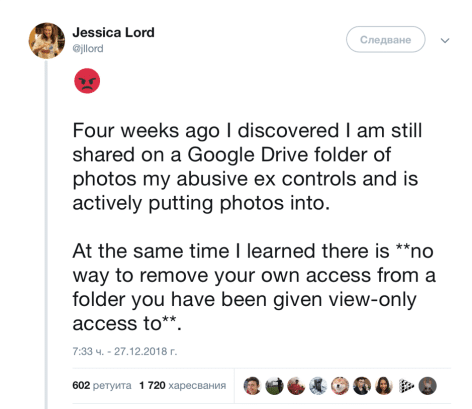
A shows that 35% of women, worldwide, have experienced violence, and 39% of women were murdered at the hands of their partner. These figures are

Healthcare has traditionally had a weaker security profile than most other industries. On the one hand, it is a favorite target for ransomware attacks, and

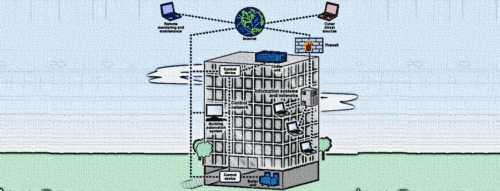
One of the most critical components of any operational entity is its data. For municipalities, data comes in many forms. It is voter registration information,

Adopting smart city technologies comes with increased risks of technical failures and cyber crime that officials must anticipate and manage, according to a guide released

If you’re anything like me, at every family and/or friends’ get-together you’ll inevitably get roped into providing free IT support for everyone’s shiny new devices. This

The battle against hackers and online criminals seems almost unfairly tilted to their advantage. After all, hackers just need to find one vulnerability, while companies
A team of researchers discovered six zero-day vulnerabilities in protocols and individual components used in smart buildings. The flaws could be used to steal sensitive
