
Why Automotive Cybersecurity Needs Real-Time Threat Detection
Automotive cybersecurity tactics and protocols will have to adapt not just to changing threats, but also to changing models of how we utilize vehicles. Automotive

Automotive cybersecurity tactics and protocols will have to adapt not just to changing threats, but also to changing models of how we utilize vehicles. Automotive

There is no doubt that cloud computing technology is now reaching all sizes of businesses and markets, offering a great opportunity for companies to achieve
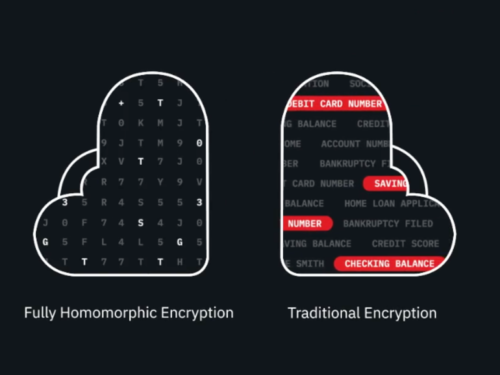
Eleven years ago,IBM made a breakthrough in the development of fully homomorphic encryption (FHE), a technology that allows for computation and analysis of data while

Fog computing, a paradigm that aims to bring cloud-like services closer to users and data sources, has become quite popular among IoT firms. Not only

Cloud computing services have transformed businesses large and small across all sectors in recent years and this is only set to increase into the new

Businesses today continue to be bombarded by an increasing number of cyberthreats, as hackers become adept at identifying and exploiting vulnerabilities in security systems. A

IoT networks are under attack, with potentially dire consequences for organizations that fail to protect them with adequate security and control measures. Last summer, the

IoT devices make our lives easier. For example, smart home technologies can optimise energy consumption conveniently by allowing us to turn household appliances on and

Dow Jones, parent of The Wall Street Journal, is among the latest companys to expose highly sensitive data, including the identities of global government officials,
Digital transformation was one of those buzzterms I heard both at RSA and during my post-conference conversations. There’s a lot of exciting changes happening on
IoT or Internet of Things has emerged as the latest trend among tech lovers. It is gradually picking up the pace and many people have

Security vulnerabilities in Microsoft software have become an even more popular means of attack by cyber criminals – but an Adobe Flash vulnerability still ranks
